Randstad, the global recruitment firm, has fallen victim to a cyber attack by the notorious ransomware gang Egregor.
In its official statement, Randstad said that defensive tactics were implemented as soon as the data breach was discovered.
“Prompt global action was taken to mitigate the incident while further protecting Randstad’s systems, operations, and data. As a result, a limited number of servers were impacted.” They said in their statement.
Investigations carried out by the emergency response teams revealed that the ransomware group Egregor was responsible for the cyber attack.
“To date, our investigation has revealed that the Egregor group obtained unauthorized and unlawful access to our global IT environment and to certain data, in particular related to our operations in the US, Poland, Italy, and France.”
Who is the Egregor group?
Egregor group operates on a ransomware-as-a-service model. They offer their services to criminal affiliates for a share of the ransom payments. The Egregor group profit to affiliate earning distribution is usually about 30% to 70%.
It is speculated that the operators behind the recently dissolved ransomware group Maze formed Egregore because their victim demographics and malware signatures are very similar.
This evidence is contrary to Maze’s claim that they do not have any successors.

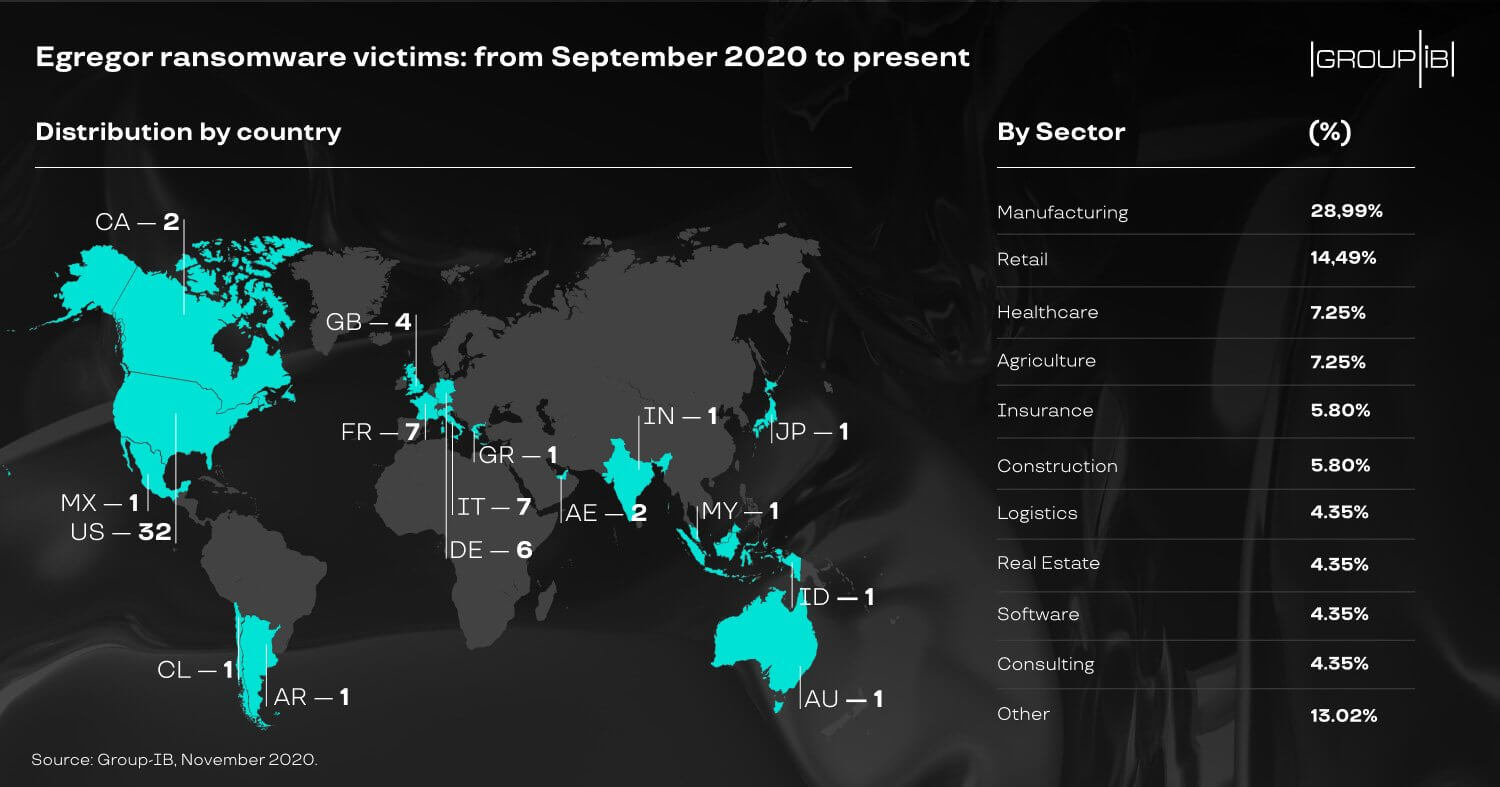
In Q4 of 2020 alone, over 71 businesses have fallen victim to the Egregor group ransomware.
Randstad is not the only high-profile victim in the past week. Kmart was the latest victim of an Egregor ransomware assault.
Ergregor operates on a double-extorsion model.
First, they encrypt all of the sensitive data accessed in the data breach and present victims with a provocative ransom note. The note demands a hefty ransom payment in exchange for a complete reversal of the malicious act.

Then, they’ll begin publishing the victim's Personal Identifiable Information to the dark web and not stop until the ransom is paid.
Randstad confirmed in its official statement that the Egregor group had already published some of its breached data.
“They have now published what is claimed to be a subset of that data. The investigation is ongoing to identify what data has been accessed, including personal data, so that we can take appropriate action with regard to identifying and notifying relevant parties.”
Egregor group victims are instructed to download a dark web browser and submit a supplied data recovery agreement via a dedicated landing page within three days.


.jpeg)








