Nissan North America has suffered a data breach exposing the source codes of its mobile apps and internal software solutions.
Hacking erudition was not a requirement in this operation. To breach Nissan’s Git server, the attackers just needed to try the default username and password combination: admin/admin.
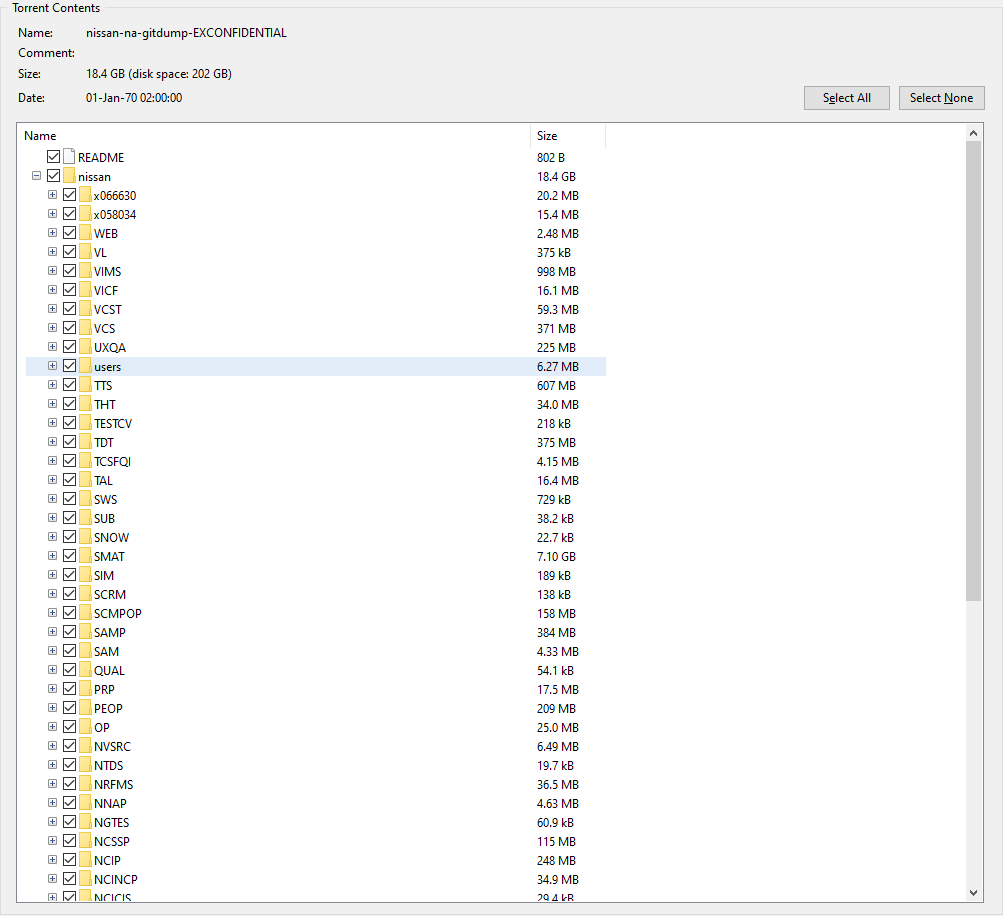
The breach exposed the following information:
- Nissan NA Mobile apps
- Nissan internal core mobile library
- Sales/marketing research tools
- Various internal marketing tools
- Client acquisition tools
- Vehicle logistics portal
- Other backend and internal tools
The compromised Git server has now been taken offline after the breached data began circulating on Telegram and hacking forums.
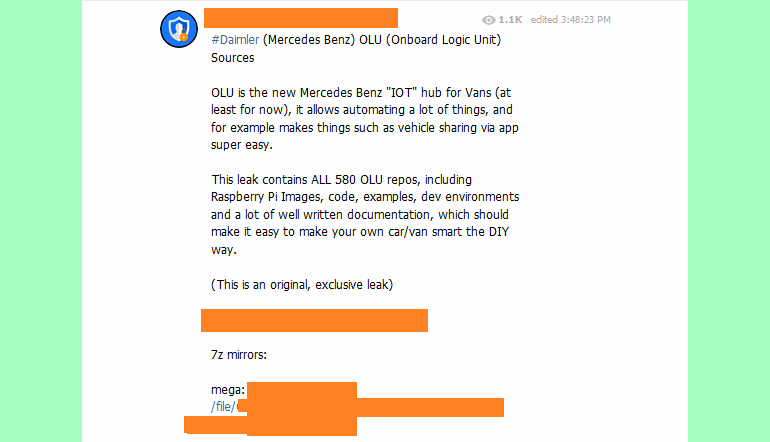
Mercedes Benz suffered a similar breach in May 2020. Daimler AG, the business behind the Mercedes-Benz brand, had its Git server breached via a simple Google Dorking operation - a process of discovering security vulnerabilities in public servers through strategic search engine queries.
These incidents demonstrate that even prestigious businesses make sophomoric security errors. Ignorance of best practices is likely to blame, a deficiency that can instantly be rectified with a sophisticated attack surface monitoring solution.










