Update 4/30/26: The article has been updated to clarify that the data leak originated from IceWarp India and pertained to its email communications with Indian customers and IceWarp HQ. Data from EU and US branches of IceWarp and their customers were not affected.
Introduction
The UpGuard Research team can now disclose that a publicly accessible Elasticsearch server belonging to IceWarp India holding more than 52 million records was discovered on Tuesday, March 24th 2026. The server contained email and other application logs relevant to both internal and client operations at the India branch of the company, with over 172,000 unique email addresses across 1,680 unique domains, just in the 10% sample analyzed. These logs included both plain text and hashed passwords for IceWarp India personnel. Internal communications between the India branch and other branches of IceWarp were discovered along with emails from IceWarp India to their customers.
Among the IceWarp India customers included in the communications are finance conglomerates Shriram and Bajaj Housing. Specific data points include the “to” and “from” pairs of email addresses for those sending and receiving the emails, timestamps, (sometimes partial) subject lines and message previews. The messages present regarded automated monitoring of internal and client resources, with reports being mailed to various stakeholders for each project. Also present are transactional emails from IceWarp India to their customers, such as invoices and contracts. The IceWarp India employee credentials pose even more of a problem, especially if the exposed accounts have elevated permissions among the hosted email systems.
About IceWarp India
IceWarp Inc., founded in 1998 and operating out of the Czech Republic, produces IceWarp Mail Server, an enterprise messaging and collaboration suite competing with products such as Microsoft Exchange and the G-Suite. Headquartered in the Czech Republic, IceWarp has five major offices around the world, including one in Mumbai, India. The exposed logs belonged to IceWarp India.
In an email to UpGuard, IceWarp confirmed that the scope of the breach pertained to IceWarp India, not other global branches:
“The office branch that this incident concerns is IceWarp India. The incident was strictly limited to email communication within the Indian branch (between the Indian branch and Indian customers/partners, or between Indian branch and IceWarp HQ). Any reference to IceWarp Inc. (US entity) or IceWarp in general is misleading for EU and US customers – European or United States customer data and main global systems were not affected.”
Data analysis
There were two types of indices present on the Elasticsearch server, daily logs averaging a couple gigabytes, and a massive 52GB “processed” log that contained an aggregate of the daily logs with some additional information. For analysis, UpGuard obtained a 10% sample of the processed log file and one of the daily logs in its entirety.
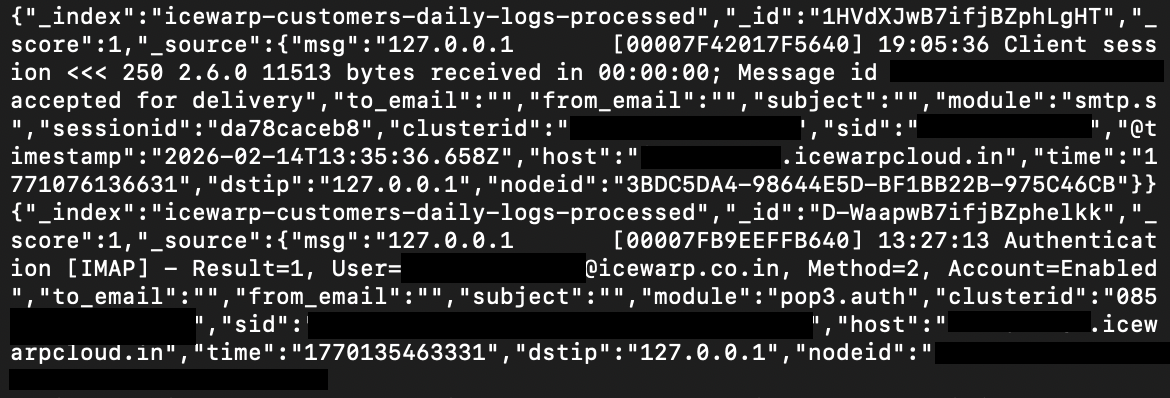
Credentials and authentication records
Two types of IceWarp India credentials were discovered among the log files:
- Plain text email credentials for 9 IceWarp India employees. These credentials were passed using the SMTP AUTH PLAIN method and thus were transferred and logged in plain text where anyone can read them.
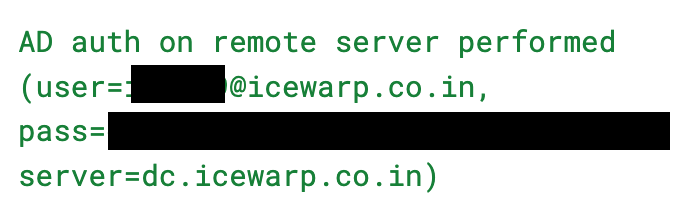
- Hashed Active Directory account passwords for 76 unique IceWarp India accounts to the domain controller dc.icewarp.co.in. The passwords appear as 32 character MD5 hashes as part of the control.adsync email authentication record. Although UpGuard did not attempt to crack any of the hashes present, MD5 is a known-compromised encryption standard vulnerable to collision attacks, meaning these hashes cannot be considered a secure protection against password exfiltration.
In addition to the credentials, the logs also contained authentication events such as successful and failed attempts as well as the remote IP address associated with the event. Dozens of internal IceWarp India users had hundreds of failed and successful login attempts, likely suggesting a brute force attack against them. W3C HTTP access logs present in the dataset also show exploitation scanning by external IP addresses against authentication endpoints. While neither of these types of attempts can be confirmed successful, the fact that threat actors were already looking at a system hosting publicly accessible credentials makes it very likely that these credentials are at risk.
Email Details
The logs originate from a Mumbai-based node in IceWarp India's cloud hosting cluster. The logs would normally be used internally by IceWarp India's operations team for server monitoring, debugging mail delivery issues, troubleshooting authentication problems, and SIEM/security event analysis.
- SMTP Logs (~73% of all records): Every email sent and received through the monitored servers, including sender addresses, recipient addresses, IP addresses, spam scoring decisions, content filter actions, and message IDs. Real email addresses from 1,680 distinct domains are embedded throughout.
- Web/HTTP access logs: W3C-format HTTP logs capturing webmail logins, download sessions, browser user agents, and client IPs interacting with mail.icewarp.co.in.
- Antispam logs: Spam scoring decisions, bypass rules, and DMARC/content filter actions for individual messages.
- Calendar and IM logs: Smaller volumes of CalDAV and instant messaging activity.
Several of IceWarp India's customers have received emails logged in the exposed data set.
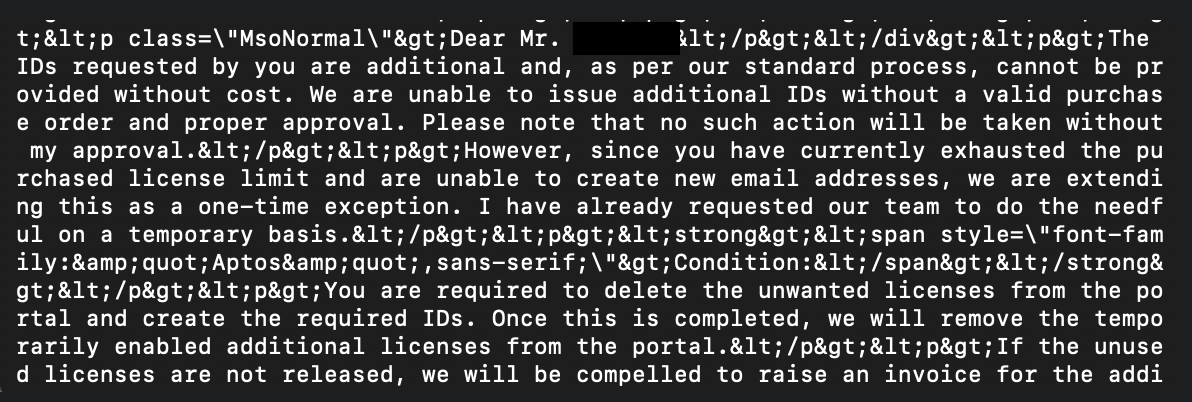
While some of these communications regard operation monitoring, email subject lines included in the logs also show references to contracts, invoice generation, POC agreements with named enterprises and pricing discussions. This indicates that business emails from IceWarp India to their clients are logged as part of this data set. Emails and replies from clients to Icewarp India are not present.
Repercussions
Email logs can reveal all types of sensitive information, from credentials, to operational details, to sensitive communication content. Hosted enterprise solutions, by their nature, outsource the risk of storing this information to a specialty provider. However, when a provider suffers a data leak, many organizations must now consider the consequences. The exposed email logs contain several layers of exposure that require attention.
- The 9 accounts with decoded plaintext passwords are fully compromised the moment a threat actor accesses this data. Given that these are IceWarp India's own employees on their own mail infrastructure, an attacker would gain direct access to the email accounts of the company that operates the platform. From inside a mail administrator's inbox, an attacker may be able to read confidential communications, intercept password reset emails for connected services, impersonate IceWarp India staff in correspondence with customers, and potentially pivot to administrative mail server functions.
- The 263 MD5 hashes from the Active Directory sync logs represent a ready-made cracking target. MD5 has been computationally broken since the early 2000s and rainbow table databases covering common password patterns are freely available. This matters because Active Directory is the authentication backbone for the entire Windows domain. Cracking even a handful of AD hashes could yield domain credentials, not just mail credentials, opening lateral movement across IceWarp India's internal network.
- 172,000 email addresses across 1,680 domains were exposed, many tied to named individuals at identifiable organizations. Combined with the authentication event logs, an attacker could see exactly which accounts were actively logging in during the capture window, which protocols they used (IMAP, webmail, SMTP), and from which IP addresses. This is everything needed to build a precision credential stuffing list: active accounts at real companies, confirmed as recently authenticated, with enough context to avoid triggering anomaly detection by matching the observed login patterns.
- The email subjects captured in the logs include internal business communications: references to contracts, invoice generation, POC agreements with named enterprises, pricing discussions, and ticket systems. Even partial subject line visibility gives an attacker enough context to craft convincing spear phishing emails that reference real ongoing business relationships. For example, a threat actor impersonating IceWarp India support to a client contact, referencing a real ticket number or a real agreement, would have a much higher success rate than a generic phishing attempt.
Under attack
Critically, the logs show that active exploitation attempts were already occurring during the capture window. One IP address was systematically probing dozens of known-vulnerable endpoints (Nacos, WordPress admin, ColdFusion, router CGI, backup scripts) using automated scanners. Another IP generated over 3,000 failed authentication attempts. These actors were already aware the server existed. The question raised by the exposure is whether any of them also accessed the Elasticsearch index and exfiltrated this data before it was discovered.
An email infrastructure compromise is inherently a supply chain attack vector. Control over mail routing or account access at an email hosting provider can be weaponized against any downstream system that uses email for authentication, notifications, or business communication.
Protect your organization
Related breaches

Student Applications: How an Education Software Company Exposed Millions of Files

By Design: How Default Permissions on Microsoft Power Apps Exposed Millions
Sign up for our newsletter
Free instant security score
How secure is your organization?





.jpg)
.jpg)
