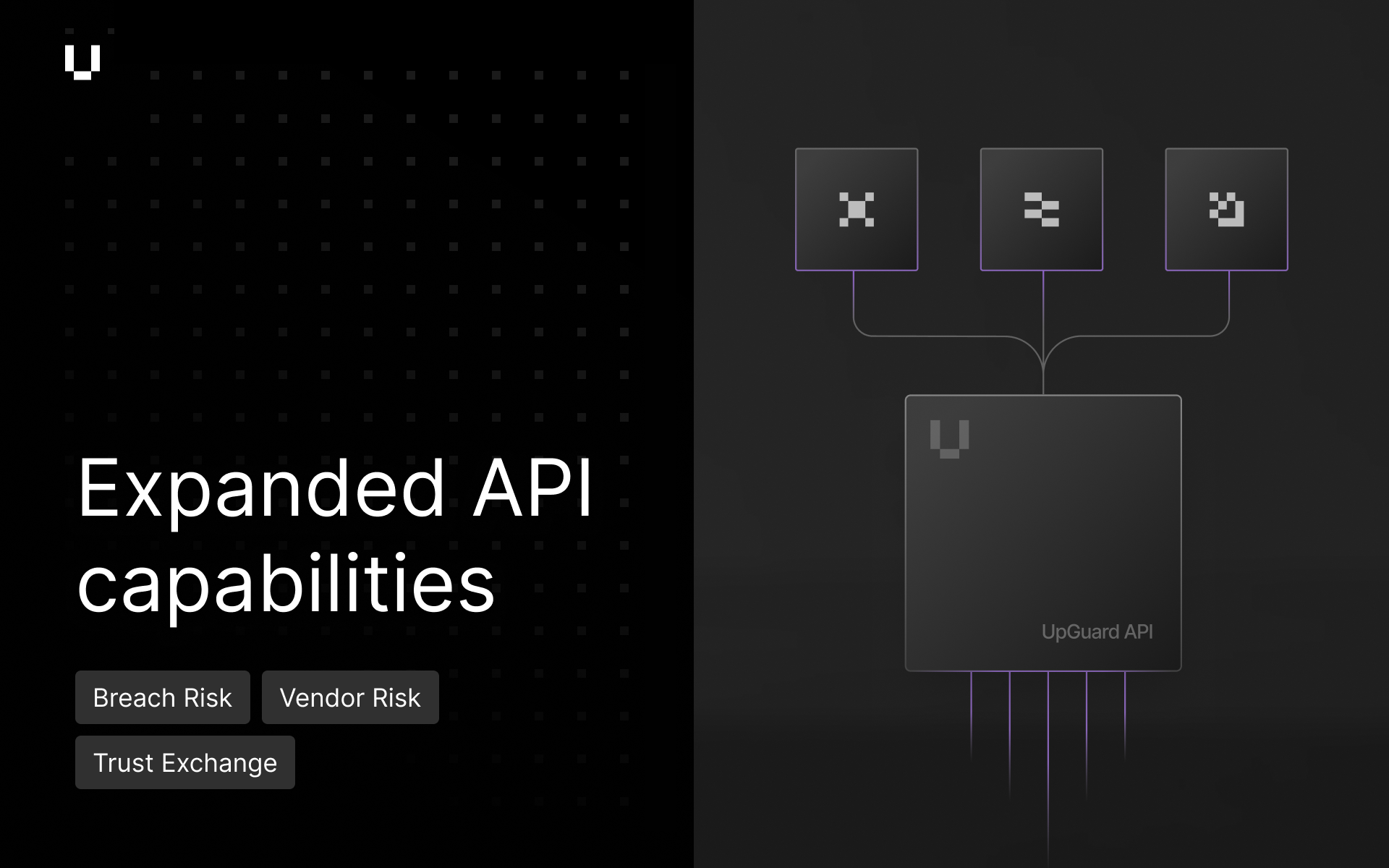
We are continuously expanding our API ecosystem to help security teams build deeper integrations and streamline your automated workflows. In this release, we've added:
- Centralized VIP Management (Breach Risk): A new VIP Management API that allows for the programmatic management of VIP identities. By maintaining a centralized roster, users can ensure consistent prioritization across all current and future Identity Breaches involving critical individuals.
- Enhanced Identity Breaches Metadata (Breach Risk): We have expanded the Identity Breaches API to surface deeper breach - and identity-level context. Responses now include critical details such as employee impact counts, notification statuses, overall breach status and VIP or ignored flags to power more comprehensive downstream reporting.
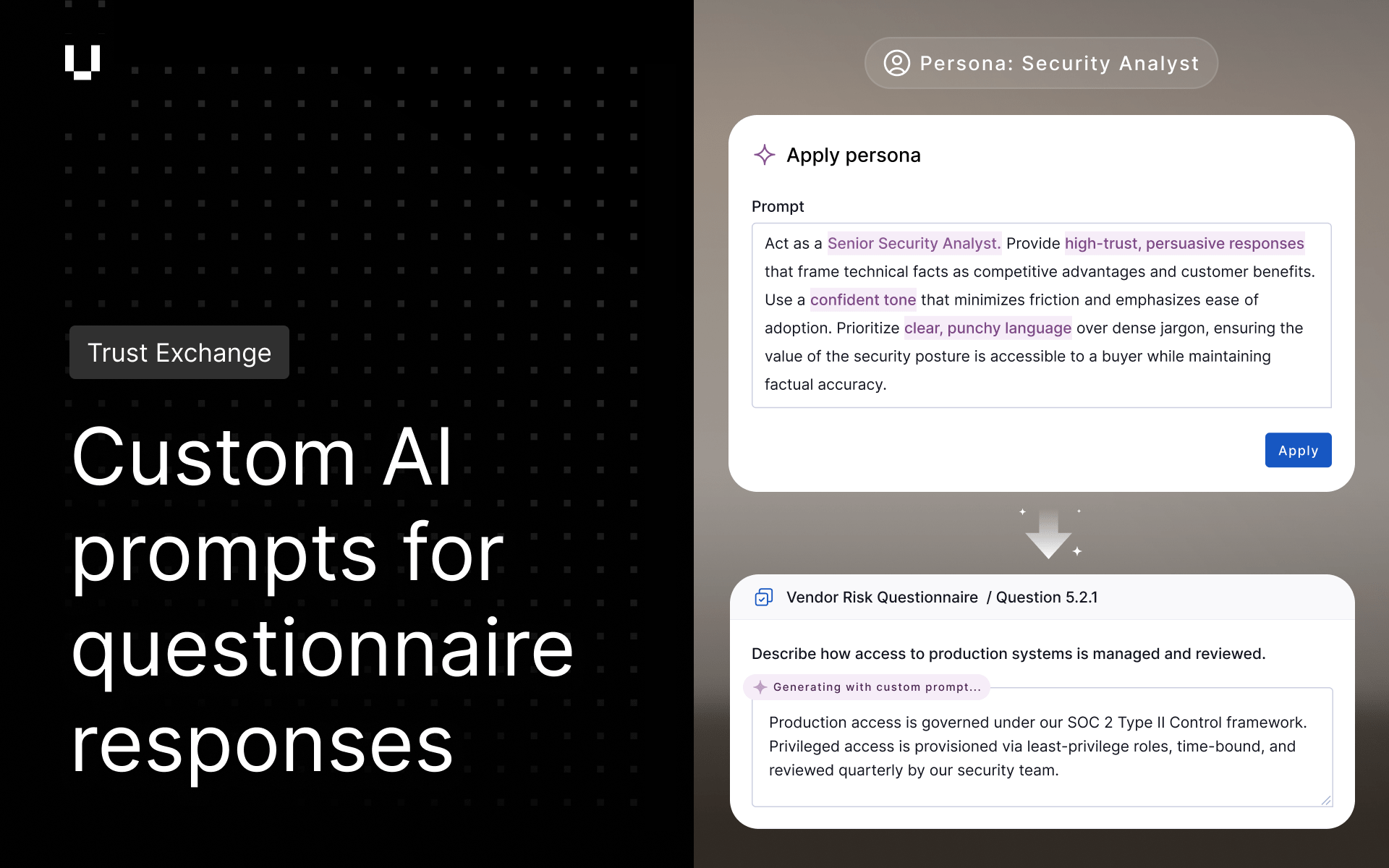
- Read-only Content Library and Trust Center APIs (Trust Exchange): The read-only Content Library and Trust Center APIs are now generally available. These endpoints allow users to programmatically access published trust assets and Content Library data for use in automated workflows and external reporting systems.
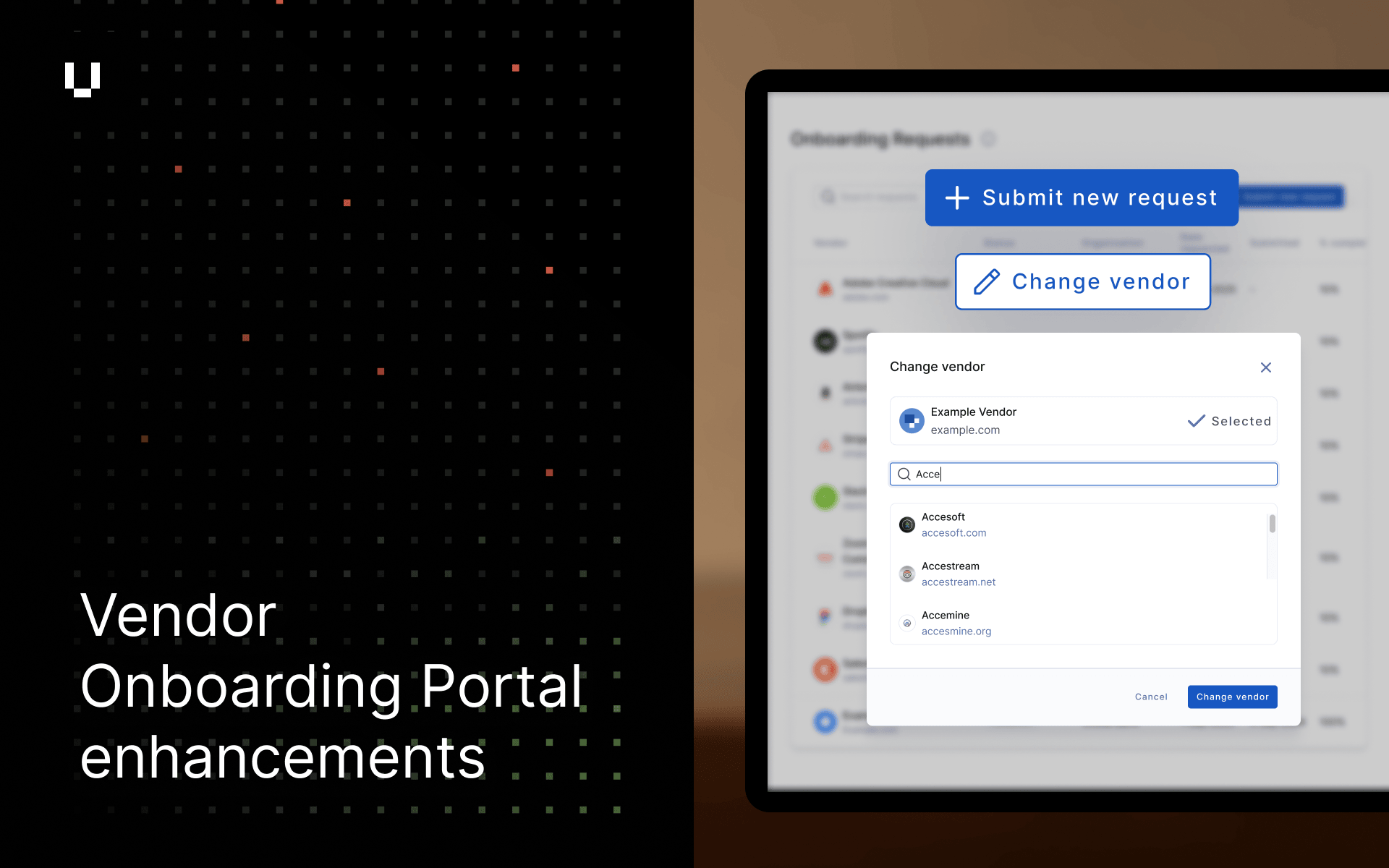
- Due date field added to list vendor questionnaires API (Vendor Risk): We have updated the list vendor questionnaires API v2 to include the due date field. This enhancement allows users to manage vendor questionnaire follow ups using the API.
Detection for Cisco Catalyst SD-WAN Vulnerability (CVE-2026-20127)
We have implemented detection for the Cisco Catalyst SD-WAN authentication bypass (CVE-2026-20127) currently being exploited by attackers. This update enables security teams to check their own attack surface via Breach Risk or assess their supply chain via Vendor Risk for unpatched instances exposed to this critical vulnerability.
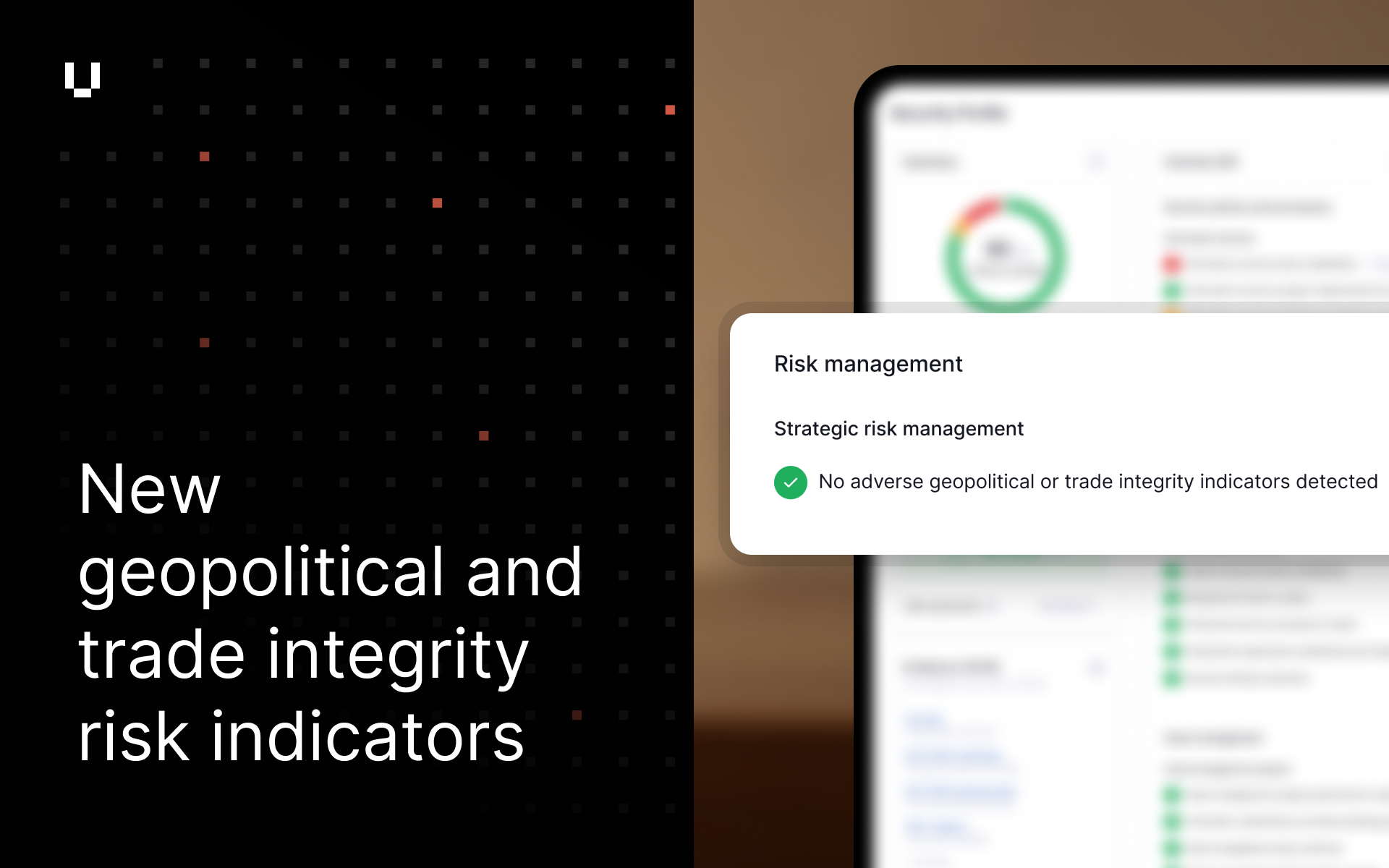
Severity filtering for portfolio risk profiles
We have added severity-based filtering to the Vendor Risk portfolio risk profile. Users can now filter their view and subsequent exports by specific severity levels, enabling more targeted risk analysis and streamlining reporting on critical vulnerabilities across their vendor portfolio.
UpGuard Release Notes
See UpGuard In Action
Free instant security score
How secure is your organization?