Cyber TPRM vs Compliance TPRM: Which is right for you?
Most organizations need both a cyber-focused TPRM platform and a compliance-focused TPRM platform, but it can be difficult to see where one tool ends and the other begins. If you're currently evaluating TPRM platforms, this guide clarifies the differences between the two.
What is a cyber-focused TPRM platform?
A cyber-focused TPRM platform provides ongoing visibility into the security posture of third-party vendors. It combines automated external monitoring with additional sources such as questionnaires, AI document analysis, threat intelligence, and more to build a comprehensive view of a vendor’s security from an external perspective. This helps organizations understand, assess, and track vendor risk over time rather than relying on point-in-time assessments alone.
Cyber TPRM platforms (TPCRM) primarily answer these questions:
- Does this vendor meet my organization’s cybersecurity risk tolerance?
- Could their cybersecurity risks disrupt our business through breaches, outages, or downtime?
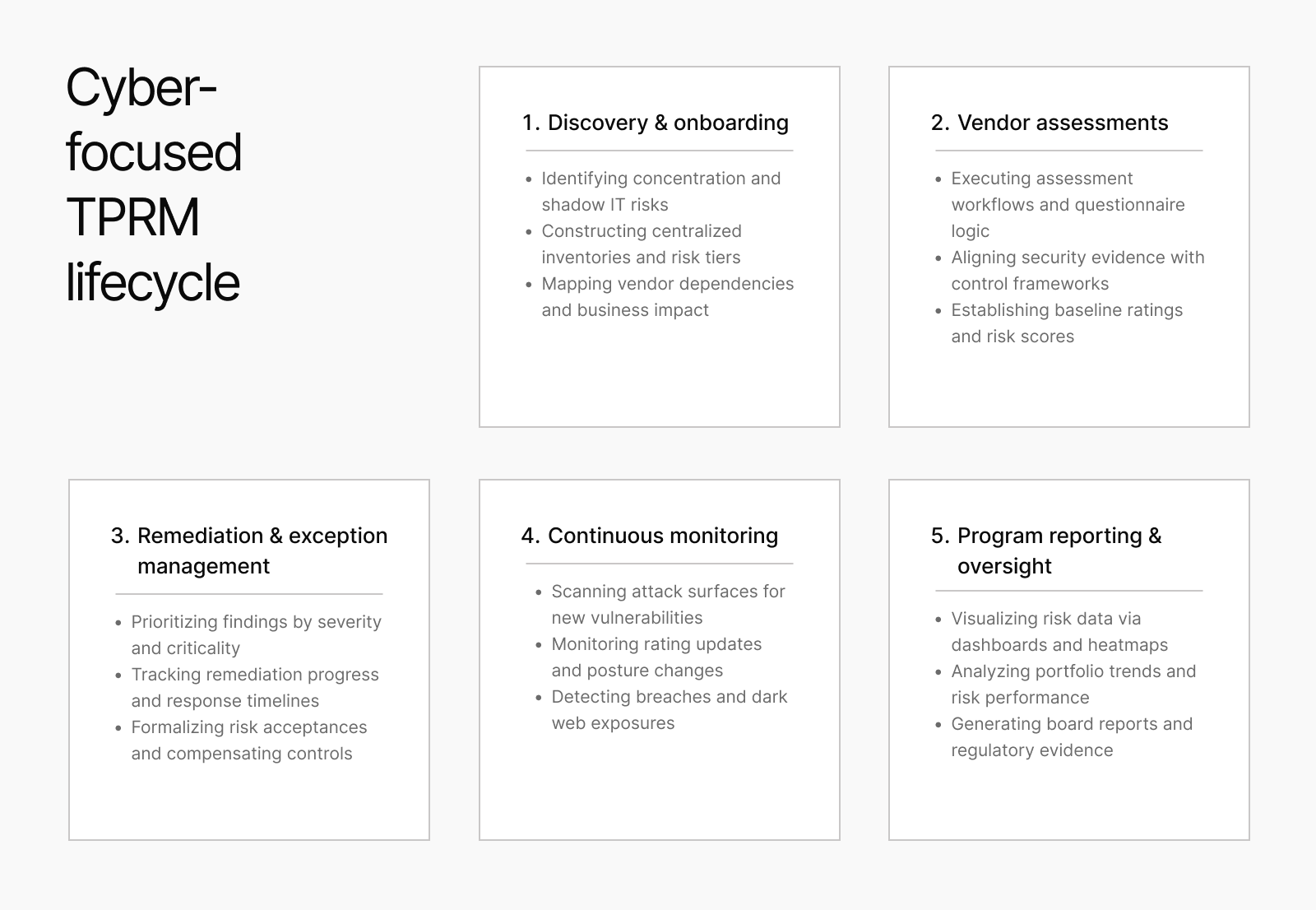
Core capabilities of a cyber-focused TPRM solution typically include:
- Vendor discovery – uncovering known and unknown suppliers through automated domain intelligence
- Security ratings and risk scoring – transforming complex security data into clear signals that track vendor postures
- Continuous cyber risk monitoring – tracking shifts in vendor security hygiene and attack surfaces through daily scans and real-time alerts
- Automated security questionnaires – Industry-aligned questionnaire templates that automatically surface risks alongside vendor responses
- Integrated remediation workflows – converting identified vulnerabilities into trackable remediation requests
- AI-Powered evidence analysis – utilizing AI to analyze security documents and public data to maintain vendor assessment momentum
- Fourth-party mapping – identifying downstream dependencies and service overlaps to reveal concentration risks across your extended supply chain
- Program oversight and reporting – generating defensible, real-time reports and board-ready summaries to communicate risk trends and demonstrate regulatory compliance
What these tools don't specialize in. If any of these capabilities are your primary buying requirement, you're evaluating the wrong TPRM platform category:
- Sanctions compliance entity screening – checking vendors against regulatory-grade global watchlists (like OFAC or EU lists) to ensure legal eligibility for business
- Ownership mapping – identifying Ultimate Beneficial Owners (UBOs) and complex corporate hierarchies to uncover hidden influence or control
- KYC/AML/ABAC workflows – performing "Know Your Customer", Anti-Money Laundering checks to verify the financial legitimacy of a business partner and Anti-Bribery/Anti-Corruption
- Negative news monitoring - tracking of credible media and public sources to identify adverse information about third parties such as allegations of fraud and corruption
- PEP checks – identifying Politically Exposed Persons within a vendor’s leadership who might pose a higher risk of bribery or corruption
- Investigation case management – providing structured audit trails and legal workflow tools to document and resolve compliance-related red flags
Primary buyers include CISOs, security operations teams, and vendor risk management leads.
What is a compliance-focused TPRM platform?
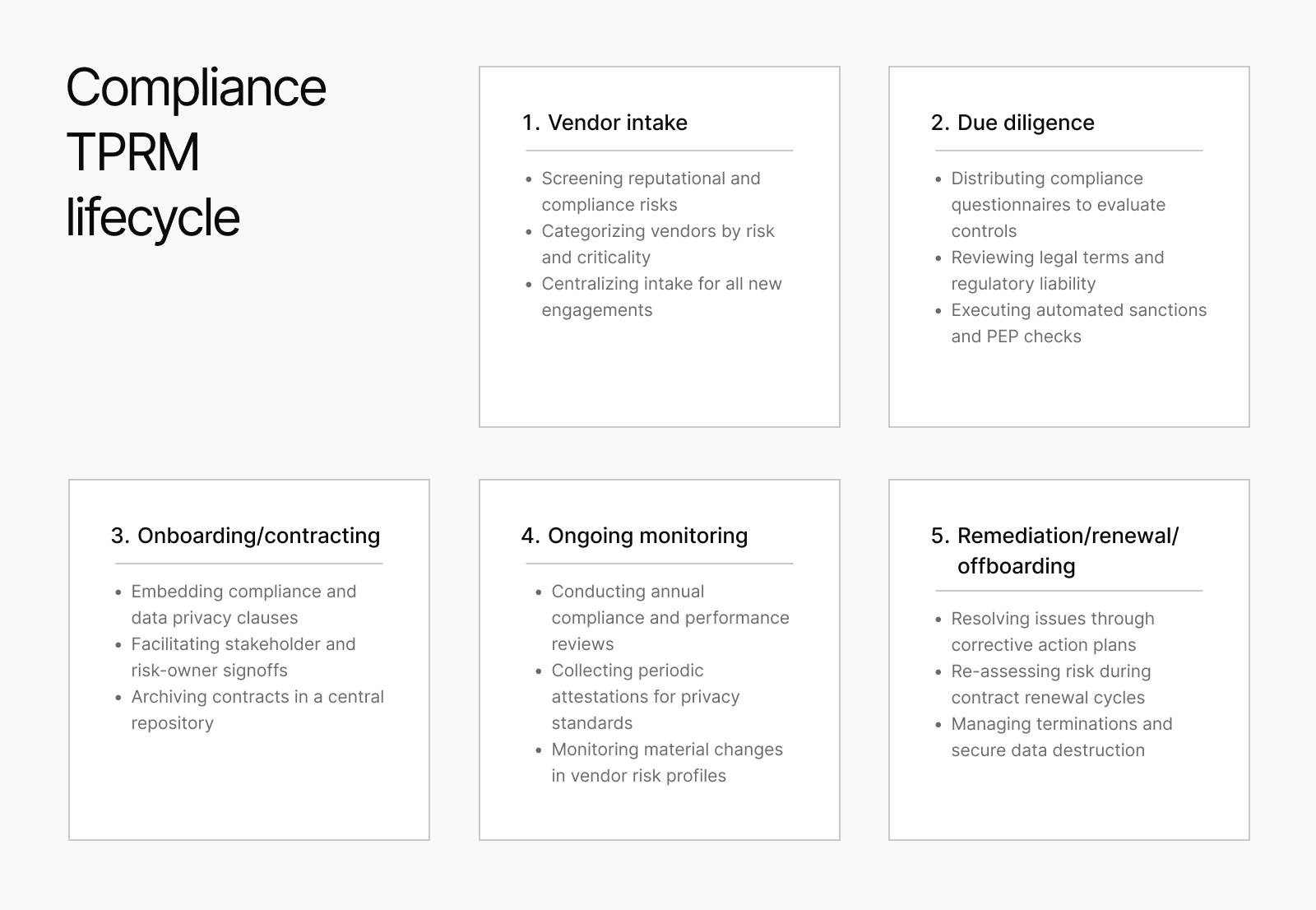
A compliance-focused TPRM platform manages vendor due diligence from the legal and regulatory angle. It handles the workflows that compliance, legal, and procurement teams need to conduct initial due diligence and continuously monitor vendors throughout their lifecycle
Compliance-focused TPRM platforms primarily answer these questions:
- Is this vendor legally and regulatorily clean?
- Are there ownership, sanctions, or corruption risks that could expose our organization?
Core capabilities typically include:
- Sanctions and denied-party screening – cross-referencing entities against global watchlists (OFAC, EU, UN) to ensure compliance with trade and legal restrictions
- Politically Exposed Person (PEP) identification – flagging individuals in prominent public roles who carry an increased risk for bribery, corruption, or money laundering
- Adverse media monitoring – scanning global news and public databases for negative press or legal issues that could indicate reputational or integrity risks
- Ultimate Beneficial Ownership (UBO) mapping – tracing corporate hierarchies to identify the natural persons who ultimately own or control an entity
- Anti-bribery and anti-corruption (ABAC) checks – vetting vendors for history or indicators of ethical violations related to frameworks like the FCPA or UK Bribery Act
- Investigation case management – centralizing red-flag documentation and remediation workflows within a secure, audit-ready system for legal teams
What these tools don't do:
- Continuous cyber posture monitoring – providing real-time visibility into the technical security health of a vendor's external-facing IT infrastructure
- Vulnerability scanning – identifying technical flaws, such as unpatched software or open ports, that could lead to a security breach
- Breach detection – searching for evidence of active or historical data compromises, such as leaked credentials on the dark web
- Security ratings – generating a numerical score or grade based on technical risk factors to benchmark a vendor's security performance
Primary buyers include Chief Compliance Officers, General Counsel, compliance managers, and procurement leads.
Where the two TPRM platform categories overlap
The confusion between cyber TPRM and compliance TPRM almost always starts in the overlap zone, not the differences.
Before dedicated Cyber TPRM platforms existed, most tools handled cybersecurity risk through manual questionnaires and static documentation. For a time, many organizations considered this sufficient.
But as cyber risk became more critical and costly, organizations recognized that InfoSec teams needed specialized tools to continuously monitor vendor security posture, which led to the category divide.
Both cyber TPRM and TPRM solutions manage vendor inventories, tier vendors by risk level, and produce risk reports for boards and auditors. Because of this overlap, buyers sometimes assume one tool covers both TPRM categories, but that’s not true.
Here's a breakdown of where the categories diverge:
Getting this wrong creates two types of blindspots:
An organization relying entirely on cyber TPRM has no visibility into whether a vendor is sanctioned, faces regulatory action, or carries export control violations.
An organization relying entirely on compliance TPRM has no signal on whether that vendor's infrastructure is vulnerable, their credentials are circulating on the dark web, or their domain security is misconfigured for phishing.
Where the gap lives
In an era of rising political tension and global conflict, a vendor’s geographic footprint is now a security signal.
Geopolitical tension often correlates with an increased risk of state-sponsored threat actors or heightened risks regarding data residency in regions with high political instability.
For example, storing sensitive data in a jurisdiction where the government exerts absolute control over infrastructure is a critical cyber risk that traditional technical scanning might miss.
Tracing these regional risks and political affiliations is essential for modern security teams. It provides the necessary context for determining the likelihood of a vendor serving as a strategic entry point for state-sponsored attacks or unauthorized data access.
How the market is responding
The TPRM market is converging because buyers need both cyber and geopolitical visibility but want to avoid the friction of managing two entirely separate data models. The goal isn't necessarily to replace dedicated compliance platforms—which legal teams still need for deep-dive investigations and UBO mapping—but to complement them.
By embedding geopolitical signals directly into the cyber TPRM platforms that security teams are already using, organizations can close the detection gap. This allows security leads to see a vendor’s regional and political risk alongside their technical vulnerabilities, providing a more holistic view of the threat landscape without forcing a tool consolidation that sacrifices depth.
How UpGuard is responding
UpGuard is responding to the market's sentiment by surfacing geopolitical insights alongside technical security data in the same vendor profile, creating a single view of technical posture and regulatory history in the one platform.
UpGuard's geopolitical and sanctions risks operate at the organization level: entity-to-entity matching against global sanctions and enforcement databases, verified by AI to reduce false positives.
What UpGuard doesn't attempt to replace is the deep compliance tooling legal teams need for UBO mapping, PEP screening, FOCI determinations, and investigation case management. That work requires different data, different legal expertise, and different stakeholder ownership.
What UpGuard covers:
Decision framework: Cyber TPRM or Compliance TPRM?
Use the following framework to work through the decision for your organization.
If your primary concern is whether a vendor's technical weaknesses could become your breach:
Start with a cyber-focused TPRM platform. This is the core function of the category — continuous external monitoring of vendor security posture, with no vendor cooperation required.
If your primary concern is whether a vendor is owned by sanctioned entities, and whether you have KYC documentation for regulators:
A compliance-focused TPRM platform is the right tool. These platforms are designed specifically for legal and procurement workflows, and they carry the data depth that ownership and sanctions analysis requires.
If you need both signals but want to start with one platform:
A cyber TPRM platform with built-in geopolitical risk signals gives the broadest single-platform coverage for security-led vendor risk programs. Sanctions and regulatory exposure surface in the same workflow as technical findings, and the escalation path to compliance tooling or legal counsel is clear when a finding requires deeper investigation.
If you already have a mature compliance program:
A cyber TPRM platform complements your existing compliance stack without replacing it. Security teams get cyber and regulatory signals in one platform. Compliance teams continue to use their dedicated tools for ownership analysis, PEP screening, and case management. The two platforms serve different buyers with different workflows — and that's the right architecture, not a gap to close.
Start enriching your cybersecurity evaluation with UpGuard
UpGuard bridges the gap between technical scanning and the complex world of geopolitical risk. By integrating geopolitical insights directly into your security workflow, you can evaluate the true resilience of your supply chain against regional instabilities and state-sponsored threats.
If you are a security team that needs to understand the link between a vendor's regulatory history, geographic footprint, and their overall cyber risk, UpGuard surfaces these signals alongside your technical findings.
.jpg)